
Photo Credit: Shutterstock

-
This week web experts discovered a huge flaw in the security software used by millions of Web sites — including many banks, email and social media services. Some sites have likened the breach to leaving your front door unlocked, and anyone who knows how to open the door can intrude and expose your confidential information.
Unfortunately, the fix isn't as simple as locking the door from inside your house. The code vulnerability exists within layers of secure Internet server coding.
 The Washington Post reported on the OpenSSL vulnerability results posted on Github.com (Image via Washington Post).
The Washington Post reported on the OpenSSL vulnerability results posted on Github.com (Image via Washington Post).
So how does this affect you?
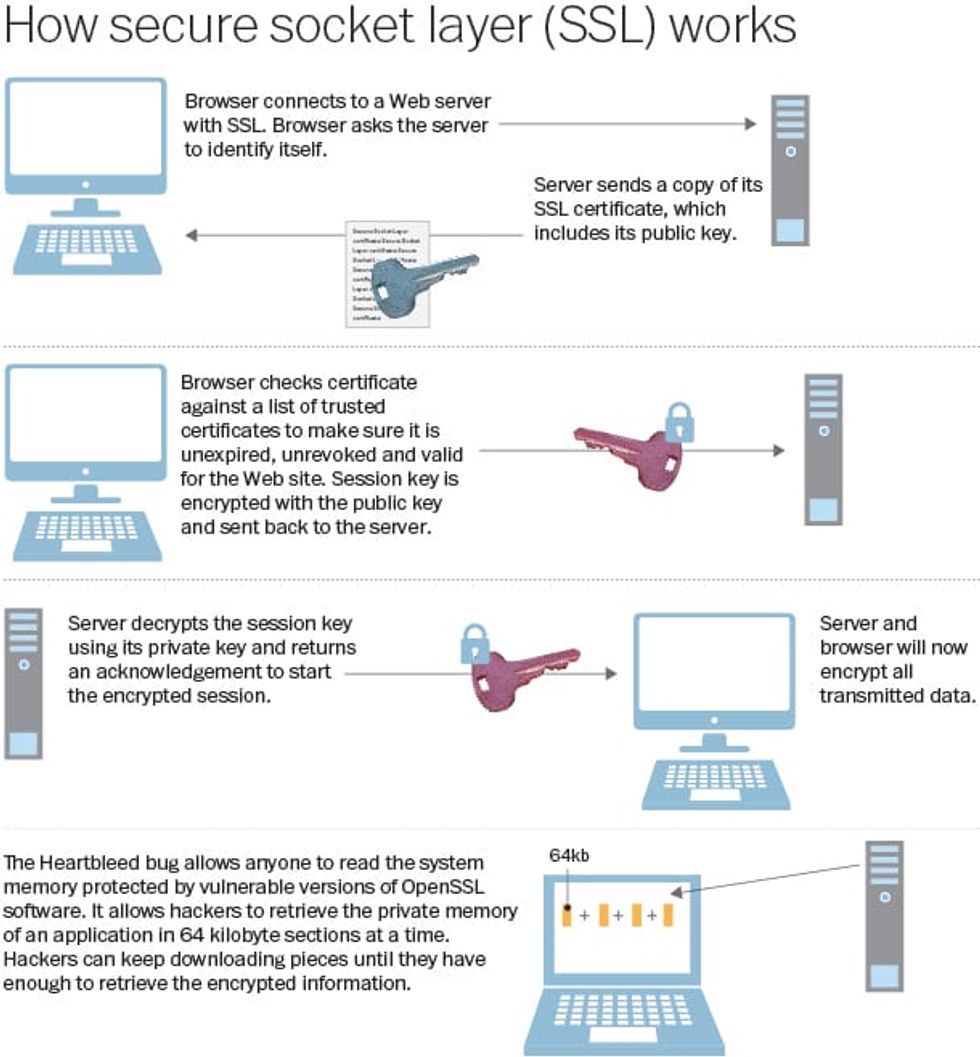
To protect web users, sites will employ Secure Sockets Layers and more recently, Transport Layer Security Internet protocols to identify and encrypt data from the user's browser to the secure end site. To achieve encrypted web traffic, a digital secure "handshake" is accomplished through an SSL or TLS Internet protocol that provide a secure channel between two machines operating over the Internet or an internal network.
The "very serious bug," dubbed Heartbleed by Internet researchers, exists within OpenSSL - the cryptographic library that is used to secure a massive percentage of the Internet’s traffic, according to TechCrunch:
"Even if you’ve never heard of OpenSSL, it’s probably a part of your life in one way or another — or, more likely, in many ways. The apps you use, the sites you visit; if they encrypt the data they send back and forth, there’s a good chance they use OpenSSL to do it. The Apache web server that powers something like 50% of the Internet’s web sites, for example, utilizes OpenSSL.Through “Heartbleed," it seems that it’s possible to trick almost any system running any version of OpenSSL from the past 2 years into revealing chunks of data sitting in its system memory.
The weakness is "in one feature of the software — the so called ‘heartbeat’ extension, which allows services to keep a secure connection open over an extended period of time — allows hackers to read and capture data that is stored in the memory of the system,” Gigaom explains.
A London-based programmer created this tool so users can check to see if their favorite Internet sites are still affected by the Heartbleed bug. Simply type in the name of your commonly-used site, Yahoo.com for example, and the results will pop up.
If a site you use still shows up as vulnerable, any hacker who understands how to exploit the weakness will have access to names and passwords, email and message content -- truly any data shared over the supposedly secure connection.
This does not mean your information has already been affected or stolen, but it does mean your personal information is vulnerable to theft until the code fix is applied to each affected server.
There is also no reason to rush to change your passwords on a particular site. “Security experts suggest waiting for confirmation of a fix,” CNET warns, “because further activity on a vulnerable site could exacerbate the problem."
More than half a million websites are vulnerable by some estimates, or two-thirds of the Internet, according to the Washington Post.
If you are in the mood for an in-depth explanation of the Heartbleed bug, check out this tutorial made by MIT Ph.D. Zulfikar Ramzan, CTO of cloud security firm Elastica.
--
(H/T: TechCrunch)
Follow Elizabeth Kreft (@elizabethakreft) on Twitter.